This post is also available in: 繁體中文
Attacks using the CVE-2023-44487 denial-of-service vulnerability, published by the National Institute of Standards and Technology (NIST) on October 10th, 2023, have been occurring over the past few months on the internet. The vulnerability takes advantage of the HTTP/2 network protocols that allow multiple streams of data to and from a server and a browser. The servers and applications that use HTTP/2 may still be vulnerable.
What is CVE?
CVE stands for “Common Vulnerabilities and Exposures.” It is a system used to identify, define, and catalog known vulnerabilities in software and hardware. The purpose of CVE is to provide a standardized way to refer to security vulnerabilities and exposures, making it easier for information security professionals and organizations to share data about these vulnerabilities. The CVE system assigns a unique identifier to each known vulnerability, typically in the format “CVE-YYYY-NNNN,” where “YYYY” represents the year the CVE was created, and “NNNN” is a sequential number.
What is CVE-2023-44487 denial-of-service vulnerability?
The HTTP/2 protocol allows clients (initiate requests to the server) to indicate that the server should cancel a previous stream by sending an RST_STREAM frame. This protocol permits clients to unilaterally request cancellations.
This attack is known as a ‘Fast Reset’ because it relies on the endpoint’s ability to send an RST_STREAM frame immediately after sending a request frame, allowing the other endpoint to start processing and then quickly reset the request.
In an HTTP/2 Fast Reset attack, clients open a large number of streams simultaneously, without waiting for the server or proxy to respond to each request stream. Instead, they promptly cancel each request.
Impact of this vulnerability
This vulnerability allows malicious users to launch DDoS attacks against HTTP/2 servers by utilizing HEADERS and RST_STREAM to send a series of HTTP requests and repeating this pattern to generate a significant amount of traffic on the target HTTP/2 server. By packing multiple HEADERS and RST_STREAM frames into a single connection, it can lead to a substantial increase in requests per second, resulting in higher CPU utilization on the server, ultimately causing resource exhaustion and denial of service.
Mitigating Attack Exposure
Lowering the limit of maximum concurrent HTTP/2 streams has been found to be effective against some exploit variants. Mlytics selects NGINX, a fully proxy server, as it provides a fundamental function for mitigating denial-of-service attacks. In the default configuration, NGINX is adequately protected by the limit of allowed requests per connection. As a result, an attacker would be required to reconnect frequently, making the attack more conspicuous and easier to stop at the network level.
Keep the keepalive_requests setting at its default value of 1000 requests. This setting limits the maximum number of requests that can be served through a single keep-alive connection. Once the maximum number of requests is reached, the connection is closed.
Similarly, keep the http2_max_concurrent_streams setting at its default value of 128 streams. This setting limits the number of concurrent HTTP/2 streams in a connection.
By relying on these restrictions, we can provide protection against such attacks by default.
Additional Suggested Mitigations
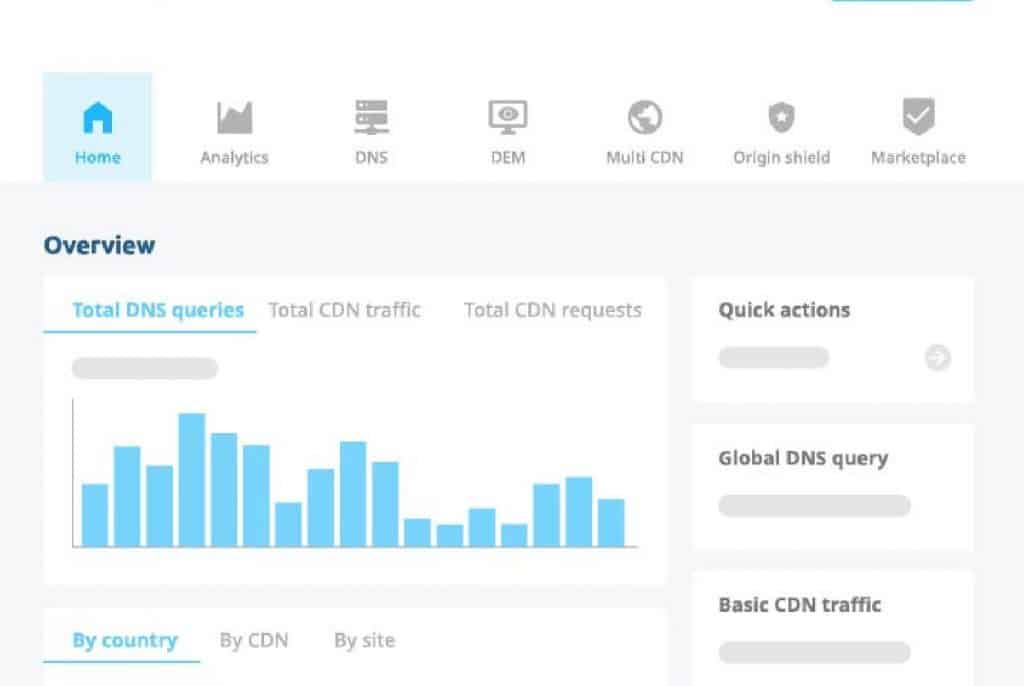
Consider implementing firewall rules with rate limiting functionality on the Origin Shield. These rules can help limit the rate of incoming requests and reject excessive requests, indirectly mitigating this vulnerability.
What’s next
So far, the HTTP/2 fast reset attack has not yielded the significant impact that the malicious actors behind it had hoped for. However, this attack technique needs to be closely monitored, as DDoS attacks continue to be a crucial tool in the arsenal of network attackers.
The Mlytics teams will continue to monitor the situation regarding this attack, investigate any variants of this attack, and update the CVE-2023-44487 advisory as more information becomes available.
References
https://www.cve.org/CVERecord?id=CVE-2023-44487
https://cloud.google.com/blog/products/identity-security/how-it-works-the-novel-http2-rapid-reset-ddos-attack